What constitutes “bring your own device” (BYOD) and what risks to GDPR compliance does it introduce?
Bring your own device allows employees to use their own devices (smartphones, tablets, laptops) in the workplace but also allows them to access corporate tools from these devices. This means they are likely to carry corporate information or confidential personal data of the company’s clients on personal, mobile hardware. BYOD could increase productivity and efficiency. Remarkably, a survey performed by Samsung in collaboration with Frost and Sullivan “Employees Say Smartphones Boost Productivity by 34 Percent: Frost & Sullivan Research” concluded that applying BYOD in the workplace could increase productivity by up to 34%. Nevertheless, this initiative carries some data protection risks as data loss can occur not only through the device getting lost or stolen but also through it getting hacked due to unsecured or unsupervised use.
Art.5.1.f) of the GDPR requires personal data to be: processed in a manner that ensures appropriate security of the personal data, including protection against unauthorised or unlawful processing and against accidental loss, destruction or damage, using appropriate technical or organisational measures (‘integrity and confidentiality’). Additionally, article 32 specifies the obligations of the controllers to ensure the security, availability and confidentiality of the personal data, three goals data protection shares with information security.
It becomes apparent therefore, that for BOYD’s benefits to be felt, companies must also implement security measures to safeguard their personal data assets.
What can companies do to support GDPR-compliance despite the implementation of BYOD?
Companies should ensure that employees are aware of the risks an unprotected or ill-used personal device poses to the security and availability of the company assets. This can be achieved through training employees about security risks, through drafting a BYOD acceptable use policy, a record-keeping policy and a security procedure policy.
When implementing BYOD, it is advisable to draft an Acceptable Use Policy, which determines the apps and tools an employee is allowed to access from their phone when they are at the workplace, the process for accessing and handling confidential data of the company as well as the reporting duties involving security concerns. This policy could also foresee the fate of the company’s confidential data stored on the employee’s phone when they leave the company and conditions for transferring data securely from one device to another. Additionally, the company should consider an enforcement process and accountability provisions in case an employee doesn’t comply with the policy. Drafting a BYOD acceptable use policy will facilitate compliance with the GDPR as it implements the principle of accountability. This principle is defined in GDPR Art.5.2, stipulating that: The controller shall be responsible for, and be able to demonstrate compliance with [other data protection principles] -and crucially with the principles of security and confidentiality introduced in Art.5.1.f).

In addition, employees should be trained and educated to understand and apply the provisions of the policy such as to use their device in a secure way to avoid hacking, as well as to keep their phone updated and secure it from data access attempts in case of loss or theft.
Moreover, a record-keeping policy ensures that the location of all company’s confidential data is known, that the data is kept up-to-date and not stored longer than necessary. As mentioned above, this practice could also ensure compliance with the principle of accountability (GDPR Art. 5,2). Some companies additionally opt for a data classification scheme, making it easier for anyone to understand the risk associated with different types of data.
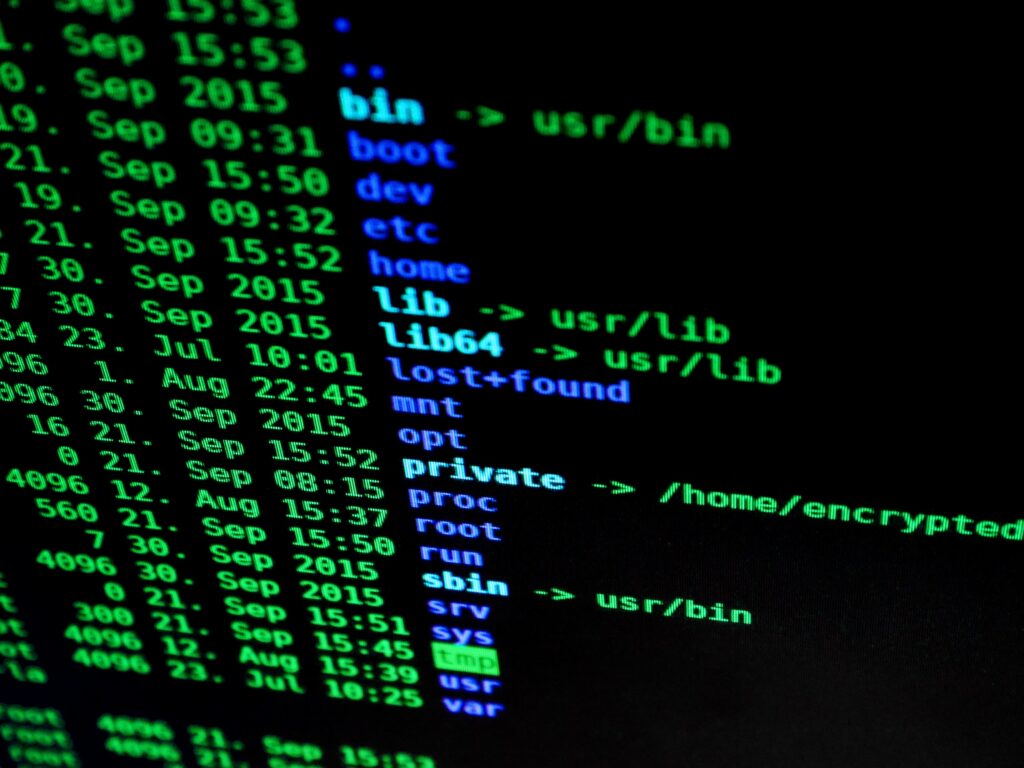
Finally, a policy outlining the security procedures should be in place, foreseeing the use of user authentication procedures when accessing applications hosting company personal data. Some companies opt for a widely-scoped access rights policy, that defines which roles require a need-to-know access and what security measures must be observed when accessing tools or datasets. Other technical measures should also be included in the policy, such as the encryption of data and the use of a firewall or the installation of anti-malware software, which helps prevent the hacking or unauthorised access to personal data in case the device is stolen, lost or compromised.
Although a wide variety of measures exist, some of them pose considerable privacy concerns, a significant one being the lack of company oversight that often results from making use of BYOD. For example, some mobile device management systems allow for the third-party tracking of the devices, the viewing of contacts, photos and videos, the reading of text messages and, in some cases, the remote wiping of data from the device. Companies therefore should pay attention to the measures they are planning on implementing as much as the software environment in use on employee-owned devices.
Conclusion
To recapitulate, when implemented wisely and accompanied by policies and security measures, BYOD can increase productivity and efficiency. Nevertheless, companies should bear in mind that a smartphone is an extension of a person’s private sphere and that this itself comes with privacy concerns. Therefore, when implementing measures to protect your company’s confidential information, you ought to tread cautiously the line between your company’s need for safety and your colleague’s right to privacy.
