There is much more to IoT security than meets the eye, especially as it concerns the GDPR. Be it for research, data collection, or consumer convenience, even the most seemingly mundane IoT devices can be unexpectedly collecting and storing what the GDPR is likely to consider personal data. Whether data is being collected unknowingly, or even just poorly protected, the opacity of any connected device, when combined with the open-ended definitions of personal data by the EU, makes for a risky business climate. There are, however, many ways to dramatically reduce this risk. Here are a few.
Understand Your Collaborators
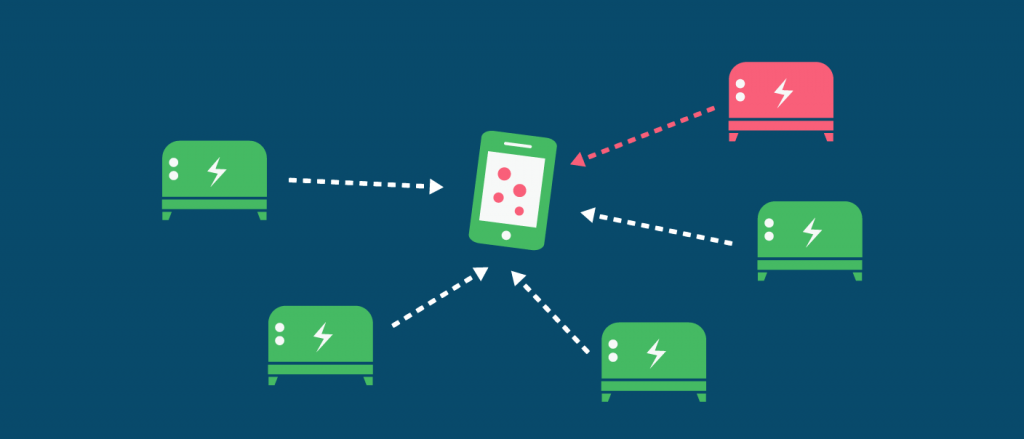
Knowing who is handling IoT security for a given device is critical. A great many IoT ventures do not work solely on their own, and require partners in order to most effectively collect, store, and analyze their data. If you are collaborating with anyone, it is important to confirm that they have these three things:
- A means of collecting consent from users if personal data could be collected by any device (even non-consumer devices may have what the GDPR considers personal data).
- Contingency plans in place for data breaches where affected people can be notified.
- Safe data storage procedures.
The best way to know if your collaborators thoughtfully understand and respond to these three needs is to already have them in place within your own organization. Here are more details regarding how to do exactly that.
Know When to Collect Consent
Sometimes the toughest part of collecting consent is understanding the context in which an IoT device may be collecting personal data. This can be more straightforward for companies that collect data from household appliances or other consumer devices where usage habits regularly equals personal data. Less clear is when connected devices are being used in areas such as research, B2B engagements and the monitoring of other machines. In a web of interconnected devices, tracing a trail of breadcrumbs back to a single individual’s ‘personal’ data and determining if you are indeed the liable party who must request their consent can be far more difficult than first expected. To address this, you will need not only legal resources, but also experts in your field who can relay unique technological constraints of a given case to those who best understand the law.

Improve Your Data Storage Methods
This step is the most straightforward. Even without the GDPR, no serious company considers reliable data security an optional measure. Though many have feared a negative impact of the GDPR on technological innovation, the incentive under new regulations to improve data storage doesn’t place a ceiling on progress, but a floor. Being transparent about actions taken as it regards security and storage procedures is also very important, even for companies that aren’t in constant dialogue with customers. It can also be tougher task for IoT ventures that don’t directly (or intentionally) handle consumers’ personal data to understand how to most effectively identify it. A science lab studying algae, for example, is somewhat less incentivized to worry about personal data on their IoT devices than a company that regularly has direct connections to customers. Nevertheless, IoT security should still be a concern in both cases.
Prepare for Breaches & Establish Plans of Action
Before even considering the damages of a data breach, consider what can be done to prevent them in the first place. For IoT security, that begins with regular software updates. Since many IoT devices are difficult to patch and are also connected to other personal devices that hold far more sensitive data, being aware of every vulnerability is a must. So, too, is allocating enough time and resources to update all devices early and often. If there is a breach, there must be an established process for identifying it, communicating the breach to authorities, and informing affected people. The administrative load for this process varies from organization to organization, but it is often best handled by a designated data protection officer.
These and other measures all contribute to not only better GDPR compliance, but also to more organized IoT security measures and more robust data management practices overall. Though there are still many other important IoT factors to consider, establishing key protocols for collaboration, data collection, data storage and data security is a solid start.
To stay up to date on how GDPR affects technology, follow TechGDPR on Twitter.
